DDS standard enables interoperability while protecting data and IP in highly connected industrial environments
Adoption of a security standard like Data Distribution Service can help to facilitate data sharing across organizations while securing wells of the future
By Mark Carrier and Reinier Torenbeek, RTI
The era of the “dumb well” is long gone. Today’s operators design and construct “smart wells” that are architected using volumes of historical data combined with high-fidelity reservoir models and advanced software techniques.
Well construction capabilities are quickly advancing due to the availability of large volumes of data, low-cost computing power at the edge and global connectivity. The value of the oil and gas digital transformation is much more than data, analytics and machine learning. It is an opportunity to create interoperability across the value chain to increase profit margins, lower operational costs and create a safer, more secure environment.
This value chain is ever expanding. The drilling process is a coordinated system of dozens of plug-and-play functions that work together to integrate machine, process and back-end business functions across dozens of plug-and-play roles. Even though the roles and data required for well construction are well understood, the industry has not agreed on a standard operational data model or set of quality attributes based on operational needs to ensure the data provenance required to make data highly actionable.
Throughout the industry, traditional closed systems have resulted in high operational costs and unscalable point solutions, and they are slowing the advances of automation that other industries have taken for granted. A network of smart wells will redefine the traditional boundaries of an organization’s enterprise systems, from the physical walls of a data center to a dynamically changing global field of operations.
Security will be the single most important requirement of these new, collaborative software integration platforms. These highly distributed, highly collaborative environments integrate third-party software applications that can introduce new opportunities for security breaches. The modern well must be protected against more sophisticated cybersecurity threats while providing the necessary access to real-time, high-quality data.
The important question that organizations face is, what actually needs to be secured? You can’t secure all data without knowing why it’s necessary; otherwise, nothing is truly secure. To properly define what data must be secure and which mechanisms to use, organizations must first define what it is they want to collaborate on and what data is required to support that collaboration.
In the oil and gas industry, well construction typically requires organizations to adhere to two security domains: operational and intellectual property (IP). Operational security includes anything that could disrupt operations, while IP security includes any data that add value to an organization or role that the organization wants to employ without giving it away.
Operational security enables an organization to collaborate in a way that will not compromise physical operations while still delivering maximum benefit. IP security creates an environment where an organization can derive value securely while protecting the organization’s intellectual property.
So how does the upstream oil and gas market transition to high interoperability while ensuring security throughout the build and operations of these highly distributed, highly collaborative and highly connected environments? There is a way to address both safety and security, as well as the need for interoperability – through the adoption of effective standards that provide proven and secure data management.
Making Data Useful and Knowing what to Secure
The digital transformation has sparked the well construction platform race to solve the problem of interoperability without introducing new security threats. However, there is no one-size-fits-all platform. An industry platform will be the integration of many platforms, so a standards approach to architecture and communications must be adopted by the industry.
To address the needs of complex, connected industrial environments, the Industrial Internet Consortium published the Industrial Internet Reference Architecture in 2015, which introduced the layered databus architecture. This is a standards-based architecture methodology and framework to develop interoperable IIoT systems for diverse applications across a broad spectrum of industrial verticals. It specifies that a secure core connectivity standard is necessary for these complex systems
The Object Management Group (OMG) Data Distribution Service (DDS) Standard for Real-Time Systems is the first international open connectivity standard that directly addresses the secure and scalable data requirements for industrial environments. DDS provides a virtual global data space where applications can securely share information by publishing information and subscribing to the information needed for a given task.
For example, a drilling optimization application may need well plan constraints, the constraints of the bit and any limitations imposed by well control. DDS data is made actionable through quality of service (QoS) attributes, which offer specific and extensive control of parameters (i.e., reliability, bandwidth, delivery deadlines and resource limits) and real-time event notifications when these contracts are violated.
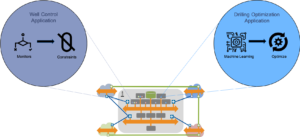
Figure 1 illustrates a reference architecture based on the hierarchical data flows required for well construction. This architecture incorporates DDS, which integrates components through data models that are defined based on the operational roles of well construction. Fine-grained security can now be applied at every point of integration and managed independently by the appropriate organization. Operational security is protected from outsider adversaries by applying cryptographic protection to the DDS network protocol. IP security is achieved by applying the principle of least privilege.
Securing Well of the Future
Traditional security models based on secured networks and encrypted data streams cannot accommodate the necessary security for next-generation operational data exchange. They either require too much trust between peers or lack the control to precisely limit access to only the information that needs to be shared across the organizations.
The modern security approach controls access to the data itself – not simply the data network – while meeting organizational policies across multiple domains. The DDS Security specification is the first security standard that targets industrial device-to-device and device-to-cloud connectivity. It is interoperable and was built for industrial-grade systems. It contains the scalability, performance, QoS and peer-to-peer nature of DDS. Moreover, it offers fine-grained access control at the data level, which controls information flow and data objects that are read or updated by a specific application.
Protection Against Outsider Adversaries
The DDS Security standard has defined mechanisms for protection of integrity and, if needed, confidentiality of information as it is communicated from producers to consumers. For this purpose, the proper symmetric cryptographic techniques are leveraged, preserving the high throughput, low latency and one-to-many (multicast) nature for which DDS is known.

The cryptographic keys used for this protection are shared only with participants that are able to authenticate with the infrastructure. Consequently, any attempt by unauthenticated outsiders to inject data or tamper with data will be detected upon reception of that data. Likewise, such outsiders will not be able to decipher any of the confidential information flows. By default, authentication happens via standard public key infrastructure (PKI) techniques, but integration with other mechanisms are allowed and possible, as well.
One challenge of any system is to keep operations running even when a malicious application is detected. By detecting unauthorized data before it enters the system, DDS eliminates that possibility. If malware were to enter the system, it would be shut down and partitioned, ensuring that operations are not affected.
Principle of Least Privilege
Even authenticated and trusted participants can be restricted in their actions of publishing and subscribing to data streams. Based on their identities as presented during authentication, access control rules define which types of data each participant may write to and/or read from. Each participant will be authorized to only perform those actions required to execute its tasks, in accordance with the principle of least privilege.
In addition to being good engineering practice, this mechanism allows for applications on the same DDS network to exchange certain information as needed but to simultaneously keep other types of data confidential. Protection of IP and separation of liabilities are among the resulting advantages.
Note that these access control rules are enforced by the infrastructure itself as part of the interaction between the participants and the data. This avoids applications having to know anything about what data other applications are (or are not) allowed to modify or observe. It also means that DDS systems that are based on standardized data models could apply standardized access control rules as well, further enhancing the level of interoperability to include security.
Configuration, not Code
At the application level, the authentication and authorization mechanisms as defined with DDS Security remain invisible. They are enabled via configuration files, including signed permissions files and governance files that define the type of protection required for each type of data.
By externalizing these aspects, different parties can more easily get an overview of which types of data are or are not accessible to which parties. This encourages collaboration where possible, without concerns of valuable information being disclosed.
Integration with Existing Security Infrastructures
Protecting the system in its entirety requires a comprehensive approach to applying the right security techniques in the right places. Examples of these are strong protection of private key material, complete PKIs with associated identity management, certified implementations of cryptographic algorithms and detection of security events.
In many cases, decisions around these security primitives have already been made at the system level, and the data distribution infrastructure will have to seamlessly integrate its security mechanisms with them. To that end, the DDS Security standard revolves around a so-called Plugin Architecture, which defines five security-building blocks. Each of those implements a standardized interface and can be swapped out by other implementations of that interface. The result is a versatile and secure information backbone.
By securing how the data moves through the system, IT organizations finally have the opportunity to standardize security policies between their IT and OT systems, regardless of the source of the data.
Conclusion
Complex architectures are extremely hard to manage, not only in terms of the architecture process itself but also in terms of getting buy-in from large numbers of stakeholders. This requires a disciplined approach to identify common architectural components and management of the commonalities between components – deciding how to integrate, what to integrate, etc.
The DDS standard has proven successful in thousands of complex, industrial-grade applications. As this article shows, DDS enhanced with security is a technology that can help address the challenges of developing modern oil and gas systems. DDS security unlocks the power of data sharing across organizations in a secure and controlled way. DC
Object Management Group and OMG are registered trademarks.




